What is Phising?
Phishing (also known as spoofing attack) is a form of cyber attack that an attacker will masquerade as a reputable unit to trick users into providing them with personal information.
Usually, hackers will pretend to be banks, online transaction sites, exchanges, credit card companies to trick users into sharing sensitive information such as: login account & password, password transaction passwords, credit cards and other valuable information.
This attack method is usually carried out by hackers via email and text messages. Users who open the email and click on the fake link will be asked to log in. If “tangled”, hackers will get the information immediately.
03 Types Popular Phishing Attacks n Crypto
What is Phishing Email?

Phishing Email is a form of phishing attack where hackers use techniques to trick you into believing that you have received a legitimate email from a known audience, asking you to provide your information. The email can be from a person or any organization you know.
For example, a Binance exchange with an email with binance.com might have a subdomain of support.binance.com. This allows the Hacker to generate an email ID that is quite similar to the Binance-related support email ID xyz@support.binance.com.
URL redirection & URL Phishing
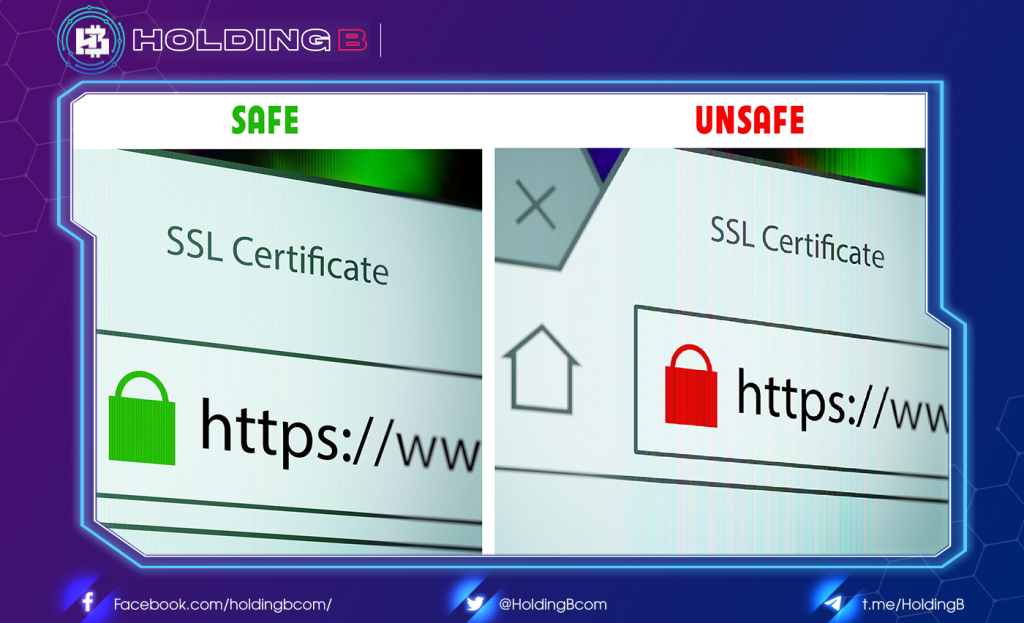
This is another common scam that hackers use to trick you into believing that you got the URL to go to the right website. The fake page is usually the login page to steal the victim’s information. They usually have some of the following characteristics:
- The design is 99% similar to the original website.
- The link (url) is almost the same as the original link. Example: reddit.com (real) vs redit.com (fake); microsoft.com (real) vs mircosoft.com (fake), coinmarketcap.com (real) vs coinrmarketcap.com (fake).
- There are always messages that encourage users to enter personal information into the website (call-to-action), then steal their information (including property).
Example: Facebook victims clicked on a manipulated link to Binance, only to find that the link pointed to www.binance-co.com, a phishing site. This site requires users to login to Binance exchange, then successfully steals their account and password
Voice Phishing

Voice phishing is also known as automated dialog fraud. Victims will be notified of abnormal activity of bank accounts, exchange accounts, credit cards, etc. Hackers are forced to confirm information to “appropriate” assets. Sometimes this type of scam is also used via SMS, asking for information confirmation.
How to Avoid Phishing Scams
As much as we all might like to live in a “trust but verify” world, none of can afford to do that anymore. The digitally interconnected world we live in today is rife with online fraud because it offers cybercriminals limitless opportunities for impersonation and anonymity. Whether we like it or not, we all must adapt our attitudes and behavior to a “never trust, always verify” approach if we want to avoid being victimized.
Recommendations for individuals:
- Be cautious about all unsolicited email and text messages.
- Hover over embedded links (without clicking) to reveal the actual URL and compare it the link that’s shown.
- Never click embedded links, even if you think they’re trustworthy. Instead, use your browser to search for the correct URL.
- Never open attachments of any kind in unsolicited email. In email from known senders, separately verify attachments before opening them.
- Use anti-virus and anti-malware on your personal devices and keep them updated.
- Use multifactor authentication on every account that offers it to prevent cybercriminals from accessing your accounts.
- Use a password manager to avoid credential stuffing attacks.
Enterprises can help to mitigate phishing attacks by implementing the following security controls.
- Conduct regular and continually updated user training; this your most powerful weapon and should not be considered optional. Train users in attackers’ latest phishing tactics and how to recognize and respond to phishing across all delivery mechanisms (email, text, IM, social networking, and malvertising).
- Deploy multifactor authentication (MFA) to prevent credentials that have been compromised in phishing attacks from being used by attackers to access other apps and resources.
- Use anti-virus and anti-malware solutions to automatically quarantine suspicious files and prevent installation of malware.
- Use a web filtering solution to block outbound traffic to phishing sites when employees inadvertently click malicious links.
- Make it easy for employees to report suspected phishing emails.
- Inspect SSL/TLS-encrypted traffic to detect encrypted malware.
- Inspect URLs within email messages to detect links to known malicious websites.
See ya in the next article !
Don’t forget to follow useful articles about Crypto Market from team Holding B !!!
- Telegram Channel: https://t.me/HoldingBcom
- Telegram Group : https://t.me/HoldingB
- Website : https://holdingb.com/
- Twitter : https://twitter.com/HoldingBcom





